“…state and non-state actors have demonstrated that acts of cyber-crime, cyber-terrorism, and cyber-warfare will continue to be increasingly disruptive threats to our complex lives…”
 A couple of months ago I spoke on the subject of cyber-threats to a small evening gathering. Because the group represented very diverse backgrounds, I focused on cyber-threats at the macro level as they impact our human future. With President Obama and this administration recently speaking openly about the relationship between National Security and cyber hacking of U.S. corporations, this subject is worthy of further dialogue.
A couple of months ago I spoke on the subject of cyber-threats to a small evening gathering. Because the group represented very diverse backgrounds, I focused on cyber-threats at the macro level as they impact our human future. With President Obama and this administration recently speaking openly about the relationship between National Security and cyber hacking of U.S. corporations, this subject is worthy of further dialogue.
Cyber-security vulnerabilities are a direct fall-out from the complexity we find in our modern information technology driven world. Unless we choose to live an isolated, self sufficient life in the mountains or deserts, our lives are dependent upon global infrastructures that are each dependent upon the information infrastructure that enables high productivity.
Just seventy-five years ago life’s primary infrastructures were only minimally interdependent. Today they are highly interdependent. As a result, global productivity has improved several-fold since the satellite and fiber telecommunications systems made it possible to touch almost every corner of our planet. This communications capacity, in turn helped usher in the era of global job markets and distributed manufacturing of goods and services. Today the flow-control aspects of energy, water, food, money, raw materials, and finished products are all critically interdependent upon the computing and telecommunication infrastructures associated with each.
 Interestingly, it was just 24 years ago when Tim Berners-Lee, while working at the European Organization for Nuclear Research (CERN), wrote his infamous paper on “Information Management: A Proposal” that created the blueprint for the World Wide Web. In that short period of time, the web has become “the” engine of global productivity. Today it is virtually impossible to find a business or government organization that operates without the aid of information technology and the interconnection of the World Wide Web.
Interestingly, it was just 24 years ago when Tim Berners-Lee, while working at the European Organization for Nuclear Research (CERN), wrote his infamous paper on “Information Management: A Proposal” that created the blueprint for the World Wide Web. In that short period of time, the web has become “the” engine of global productivity. Today it is virtually impossible to find a business or government organization that operates without the aid of information technology and the interconnection of the World Wide Web.
However, like all complexity growth, the cost of productivity gain is the counter-productive opportunity for crime and disruption. This was the case when man invented basic tools, and as these tools graduated into continental and global infrastructures, like rail lines and shipping lines, criminal and military operations emerged to exploit the new complexities. When taken as a whole, the World Wide Web and the billions of associated computing resources, represents our planets greatest complexity. It is, therefore, not a stretch to understand that cyber-threats are the most complex form of threat the world has known, to date.
 To restate this more succinctly–life has evolved by what some call the law of rising complexity. Shared information is the enabling foundation of complexity as we have learned in biology-complexity, ecology-complexity, and now socioeconomic-complexity. Rising complexity enables opportunities for new threats. Cyber-threats represent the greatest opportunity to disrupt our modern socio-economic way of life and will remain so until a higher form of complexity emerges.
To restate this more succinctly–life has evolved by what some call the law of rising complexity. Shared information is the enabling foundation of complexity as we have learned in biology-complexity, ecology-complexity, and now socioeconomic-complexity. Rising complexity enables opportunities for new threats. Cyber-threats represent the greatest opportunity to disrupt our modern socio-economic way of life and will remain so until a higher form of complexity emerges.
Cyber-threats are fundamentally about three things;
- Intercepting information in motion so that it can be stopped, diverted, or changed;
- Accessing information at rest so that it can be stolen, modified, or erased; and,
- Denying cyber services by overwhelming the information infrastructure so that information can not be accessed or delivered.
High-level examples of all three attack vectors have been seen over the past few years. For example, denial of service attacks disrupted the Country of Estonia for several weeks in April of 2007, intercept attacks may have been responsible for 15% of the world’s internet traffic being routed to Chinese computers in November of 2010, and over the past two years Chinese hackers have uploaded the Department of Defense’s F22 and F35 fighter blueprint data from defense industry computers.
In this Country concern for cyber-threats has been on the rise over the past two Presidential administrations. During his recent State of the Union address in January, President Obama stated, “America must also face the rapidly growing threat from cyber-attacks.” Just this month President Obama’s National Security Advisor, Tom Donilon delivered a stern message to China stating that, “The United States will do all it must to protect our national networks, critical infrastructure, and our valuable public and private sector property.”
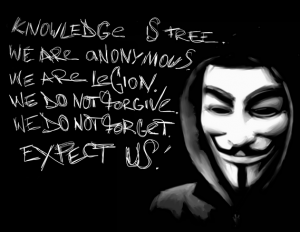 Criminal and National Security cyber attacks are not the only outlet in the world of cyber-threats. Hacker-terrorist groups are using hacker tools and techniques to deliver political and social messages, and to deliver damaging retribution against businesses and governments. A recent You Tube post by the hacker group “Anonymous,” warns the people of the U.S. against the demise of our Country brought about by anti-constitutional government actions, and leaves open the possibility of cyber-attacks against our government institutions.
Criminal and National Security cyber attacks are not the only outlet in the world of cyber-threats. Hacker-terrorist groups are using hacker tools and techniques to deliver political and social messages, and to deliver damaging retribution against businesses and governments. A recent You Tube post by the hacker group “Anonymous,” warns the people of the U.S. against the demise of our Country brought about by anti-constitutional government actions, and leaves open the possibility of cyber-attacks against our government institutions.
Shifting subjects slightly, this April in San Diego, at the Armed Forces Communications and Electronics Association (AFCEA) symposium, I will moderate a panel of experts in a discussion on the subject of Information as a warfare area. Warfare area in this context means an area of warfare that has become formalized and evolved through a cadre of dedicated military personnel, processes and material systems to more effectively wage war in that area. For example anti-air and anti-submarine warfare are the outgrowth of the introduction of airplanes, missiles, submarines, and torpedoes as instruments of war.
It should be a lively discussion…
…by definition, state and non-state actors have demonstrated that acts of cyber-crime, cyber-terrorism, and cyber-warfare will continue to be increasingly disruptive threats to our complex lives…
… and therefore, it will require dedicated resources to counter these vulnerabilities.

Marv:
Good write-up. Some additional thoughts…
Cyber is unlike most environments we are used to operating in, which has made the translation of strategy and tactics difficult. For example, when dealing with bad actors in the physical domain, we often use the combination of confirmed identity and geographical containment to inhibit their activities. We use various surveillance techniques to make a positive identification, then establish check points and other filters to restrict their access and movement. In cyber, we seldom can establish an identity beyond the physical device used as an access point, and as that is not physically tied to a person or location, can easily be relocated or replaced. Because of this fluid hardware component, we have no means for containment except in a very gross and disruptive way.
In many ways, we need to take a step back and rethink the methods and means by which we consider cyber. We have a similar situation in Iraq when we didn’t understand the nature of the IED threat. Now, as we did then, we need to think about the problem holistically, from the fabric of transmission to the role of international law. Too many people are reacting to the latest attack signatures and target sets, and not thinking about the strategy for winning the war. Where is that conversation taking place?
Regards,
Todd
Todd, great comments. Like so many things in our world, we seem to not be able to correct foundational technology after it has taken a strong foothold. But I agree with your “step back” approach to working these issues…
Marv …as always a great perspective…and right on the mark. Recently I spoke at Virginia Tech on change …with a major focus on CYBER. Clearly that generation are natives of that world and prepare themselves daily to win in that world. Having been a “CYBER fighter pilot” my entire career …I expect like so many other warfare areas …many will say (like the infantry, Calvary over the aviator (in the 1920s)) cyber warfare leadership is best in the hands of space and aviation leaders. But the only way for real discussion needs to come from the those that create the information technology, manage it and defend it…they are the true CYBER warriors.
Thomas, thanks for the spot on comments. As Todd says, it is time that we take this issue seriously and begin the real work.
I have to append this eloquent response I received by email from the mentor of most of us information warfare students, ADM Jerry Tuttle:
“One cannot really understand the real significance of this new emerging cyber warfare as a weapon until you hear it described with the power and imagery of Dr. Marv Langston. Marv possess the eloquence of diction, the imagery of poetry and the brilliance of metaphor to describe in precise detail the new vistas that cyber warfare brings to the alter. He has masterfully avoided steering by the wake and approaching the obvious with statements of discovery as he sagaciously provides a pellucid vision for cyber warfare
Warm regard,
Jerry”
Marv,
My thought is that one way to deal with complexity is to try to simplify some aspects of it down to core tenants. Susan Lawrence, the Army G6, has put her focus on addressing the first two of your bullet points. The Army networks cannot be made invulnerable. The most important thing is to protect the data that uses those networks for transit. Data at rest is the highest priority and needs to be addressed from multiple perspectives , not just building thicker walls around data storage. One of the key elements is using the cloud to significantly reduce the number of places where data is at rest by using thin client applications that have no data stored locally. These are not ideas that I take any credit for, only my understanding of what LTG Lawrence and her Deputy, Mike Krieger, have talked about recently. My view is that the Army seems to be in full agreement with your blog and is trying to simplify the complexity of their data so they can better protect it.
As expected, I cannot make a meaningful contribution to this masterpiece that resides on the ether side of Pluto intellectionally. This same brilliance needs to be applied to creating a culture of ethics, trust, and integrity. Those creating the process and procedures for this change are making recommendations that even if flawlessly implemented would be as effective as taping an aspirin to one’s forehead. Marv, needs to have the freedom to be creative and the guidance to be effective. I am honored to have him as a friend.
Marv,
You have hit the nail on the head.
“Rising complexity enables opportunities for new threats. Cyber-threats represent the greatest opportunity to disrupt our modern socio-economic way of life and will remain so until a higher form of complexity emerges.”
And yet we are spending less on offensive and defensive IA than countries like Iran. Very scary.
Dave
Marv
Excellent capture of the essence of the complexity of the present ‘ecosystem.” 2013 may be shaping up to be an inflection point for policy responses, which may assist in providing the “dedicated resources” you call for:
–Tallinn Manual on Customary Law of Armed Cyber Conflict, setting out boundaries of expectations among a community of legal scholars, including DoD community, for rules of engagement, just published –finally, after years of reports and gnashing of acquisition community solutions, a statement from the U.S. Congress in Sec. 516 of the new Continuing Resolution addressing ICT Supply Chain hygiene –the new Executive Order from the Administration which, with a little lucky alignment of DHS and NIST asters, may get private sector Critical Infrastructure participation in efforts to shore up cyber security across a broader swath and with more effective investment than heretofore…
Marv,
Great post and I apologize for the late reply. In my mind another important point is the economy. There are numerous companies (such as mine) that have global headquarters in the United States but also have manufacturing operations in China. I wonder if a study has been conducted on the number of companies with facilities inside China that have experienced cyber “issues” coming from China touching the US part of the business?
Kind Regards,
Joe
Marv,
As always, I feel smarter when you share your thoughts. I think there are lessons learned throughout the history of warfare that should be remembered when trying to protect our networks. In situations where the threat is unacceptable, it is sometimes better to maneuver rather than slug it out. An example might be learned from how the fleet operates with NGOs. We don’t allow the cooperating organizations access to NIPR; instead we stand up a non-classified enclave. The same tactic could be applied afloat for social media etc.; NIPR machines would not be open to the internet but a non-classified BYOD enclave would allow each sailor to access the internet with his or her own device. This might be an inconvenience but we accept inconveniences in the name of security all the time.
V/R
Alex