Jim and I have now completed six thirty minute webinars that are posted on this site, YouTube, and Linkedin. Here is a short introduction to these webinars. We find these discussions to be very informative and relevant to the challenges of today. Please let us know your thoughts.
Podcast #6 guest discussion is with DoD acquisition expert, Bill Greenwalt, who discusses his Congressional Staff work that helped make Other Transaction Authority contracting available for all programs of record within DoD and also delivered the Covid-19 vaccine in record time.
Also, please take a look at Bill’s recent Hudson Institute paper — Competing in Time: Ensuring Capability Advantage and Mission Success through Adaptable Resource Allocation. This paper addresses the budget process “elephant in the room” for U.S. Military capability over time.
Podcast #5 guest discussion is with Zero Trust and 5G expert, Junaid Islam, who discusses how the future of 5G presents even greater cybersecurity challenges for the future.
Podcast #4 discussion is with guest blogger Evan Dudik, an expert China analyst, who walks us through his research and views on how China is working to influence global trends and how that relates to U. S. National Security.
Podcast #3 guest discussion is with AI expert Todd Carrico who discusses his views on where AI is today relative to the past. Todd is the developer of a multi-agent AI platform to support Defense logistics.
Podcast #2 guest discussion is with We discuss how China has emerged as a peer competitor to the U.S. particularly in the Pacific region.
Podcast #1 guest discussion is with Ken Tirman who discusses some of the biggest challenges for our Nation and the planet in today’s accelerating technology world.
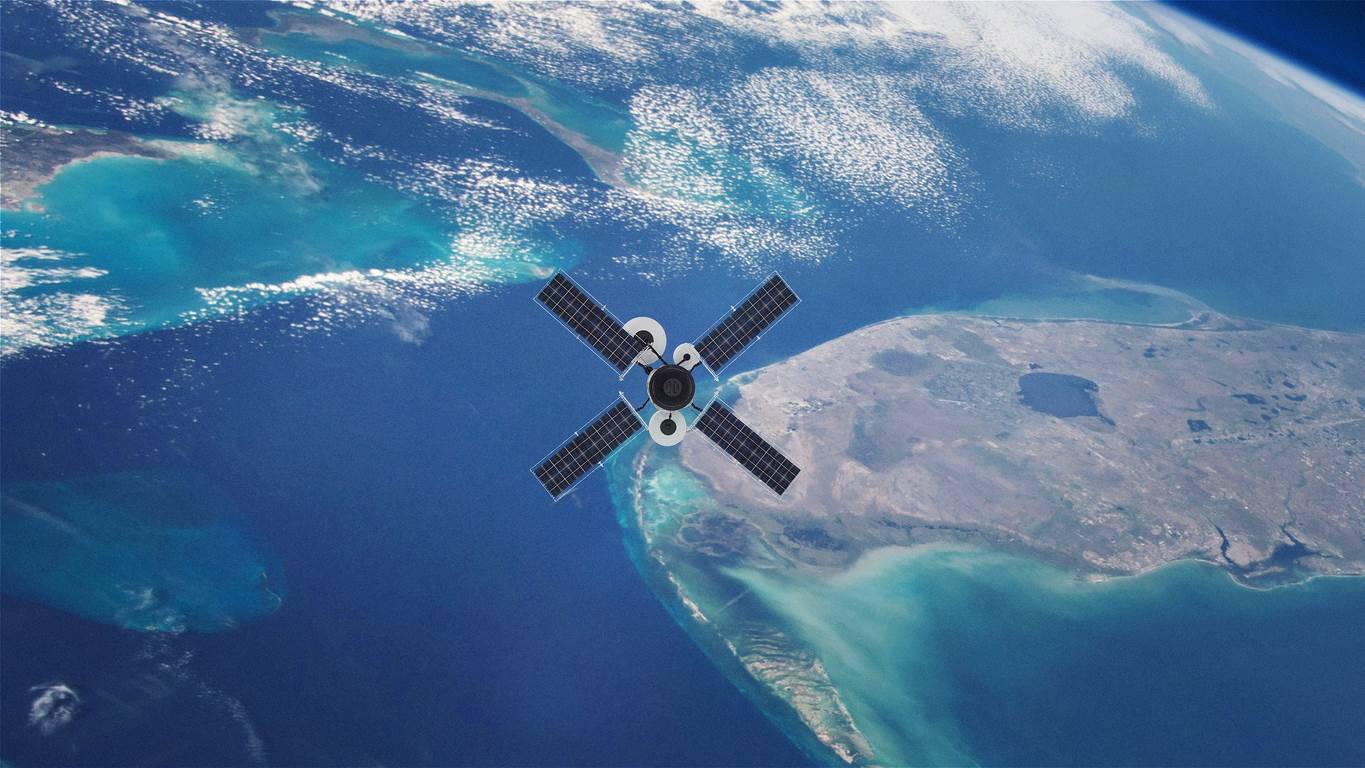
I have also posted my June 15th San Diego AFCEA luncheon talk on the future of Navy ship-to-shore and ship-to-ship communications when Starlink’s low earth orbit (LEO) internet communication satellite constellation has 12,000 satellites on orbit by 2027.
If you have ideas on topics or guests you would like to hear from please leave a comment or send Jim an email at jim@pietrocini.com or marv@marvlangston.com. You will also find a short bio on each of our guests under the Guest Bio’s pulldown.

 We all know that information about our adversaries and partner countries is and always has been critical to National Security. Before our interconnected world of the internet, information operations were more about human spying, one person to another. As technology has progressed this information criticality has only become more intense, and today has become the most critical component of modern warfare.
We all know that information about our adversaries and partner countries is and always has been critical to National Security. Before our interconnected world of the internet, information operations were more about human spying, one person to another. As technology has progressed this information criticality has only become more intense, and today has become the most critical component of modern warfare.